Once user hot wallets were stolen, the maker of bitcoin ATMs shut down its cloud service.
The maker of Bitcoin ATMs, General Bytes, claimed that a hacker was able to set up and run a Java program on their terminals, giving them access to customer data and allowing them to transfer funds from hot wallets.
General Bytes, a company that makes Bitcoin ATMs, has shut down its cloud services after identifying a “security vulnerability” that enabled an attacker to access users’ hot wallets and acquire private keys and passwords.
The company, a maker of Bitcoin ATMs, is situated in Prague and claims on its website to have sold over 15,000 ATMs to 149 different countries.
The ATM manufacturer published a patch release bulletin on March 18 stating that a hacker had been able to remotely upload and run a Java application via the master service interface into its terminals with the aim of stealing user information and transferring funds from hot wallets.
On March 17-18th, 2023, GENERAL BYTES experienced a security incident.
We released a statement urging customers to take immediate action to protect their personal information.
We urge all our customers to take immediate action to protect their funds and https://t.co/fajc61lcwR…
— GENERAL BYTES (@generalbytes) March 18, 2023
This lets the hacker accomplish the following, according to General Byes founder Karel Kyovsky’s explanation in the bulletin:
- “The potential to access the database.
- Having the ability to read and decrypt the API keys required for obtaining funds on prominent exchanges and wallets.
- Transfer money from hot wallets.
- Turn off 2FA and download user names and password hashes.
Having the ability to look through terminal event logs for any instances where users scanned private keys at an ATM. These details were being logged by earlier ATM software versions.
Both General Bytes’ cloud service and other operators’ standalone servers were compromised, according to the alert. Since 2021, Kyovsky stated, “We’ve completed a number of security audits, but none of them detected this vulnerability.
Compromised Hot Wallets
Although the company mentioned that the hacker was able to “Transfer funds from hot wallets,” it did not specify how much money had been stolen as a consequence of the incident.
General Bytes, on the other hand, disclosed the specifics of 41 wallet addresses that were utilized in the hack. According to on-chain statistics, there were numerous transfers into one of the wallets, leaving a balance of 56 BTC, or more than $1.54 million at the time of writing.
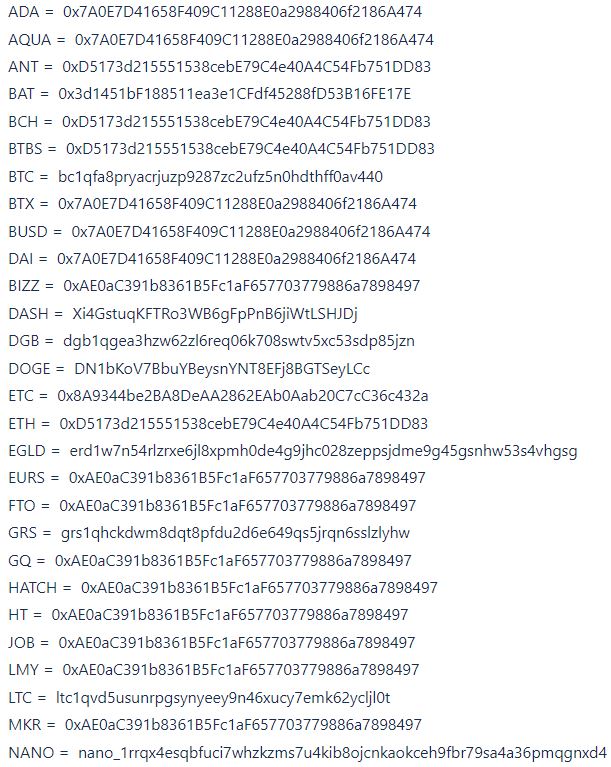
Another wallet shows a number of ETH transactions, with a total receipt of 21.82 ETH, or about $36,000 at the time of writing.
The company has provided two fixes for their Crypto Application Server (CAS), which controls the operation of the ATM, and has urgently recommended BTC ATM operators install their own standalone servers.

“Please keep your CAS secured with a VPN and firewall. Terminals should use VPN to connect to CAS as well “Kyovsky wrote.
” Additionally, consider that the API keys, exchange passwords, and hot wallet passwords of all your users have been compromised. Please invalidate them and create new passwords and keys.”
In September of last year, a zero-day attack on General Bytes’ servers allowed hackers to take over as the default administrators and change settings so that all funds would be transferred.
Also Read:
Bitcoin ATM Rise Or Fall: In Less Than 60 Days, More Than 400 Machines Went Offline













Discussion about this post